Secure DevOps: How to make security integral into your DevOps process
|
Secure Devops: Learn how to make security integral into your DevOps process.
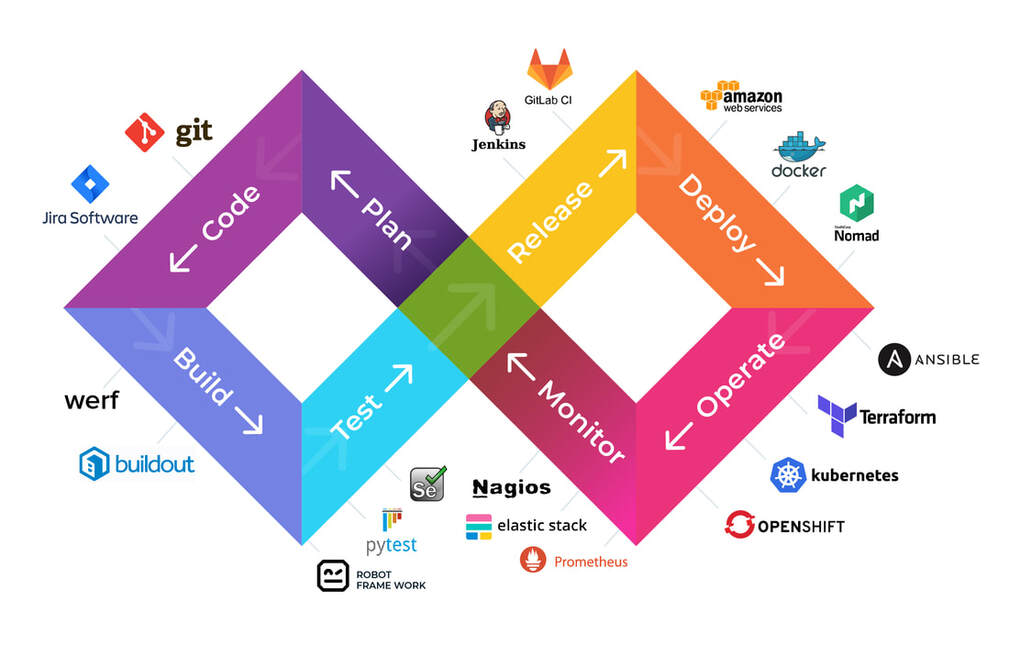
DevOps driven software development approaches are pervasive among organizations embracing cloud. Unlike traditional software development approaches, DevOps helps organizations shorten the time to build and ship cloud applications. Introducing security early into the software development lifecycle along with continuous monitoring in production environments improves the overall security posture of cloud applications reduces business risk. Although there is increased awareness among cloud adopters to embed security early in the software development lifecycle, many organizations are challenged to incorporate security with an automated approach. For these organizations, risk management is an afterthought that begins once the software is in production, and thus innovation is often stifled and time to market slowed. Prisma helps you mitigate known security issues early in the software development cycle with open security APIs and automated security controls that integrate into your CI/CD pipelines. It accelerates your journey to the cloud by providing unprecedented risk visibility as well as consistently governing access, protecting data, and securing applications. |
|