|
Revolut, a leading fintech company, recently experienced a highly sophisticated cyberattack resulting in the unauthorized extraction of over $20 million. This breach serves as a powerful reminder for organizations to remain vigilant against evolving cyber threats. In this article, we explore the breach, highlight effective cybersecurity practices, and emphasize the importance of comprehensive defense strategies.
Exploiting Weaknesses: The cybercriminals skillfully manipulated a flaw within Revolut's payment systems, exploiting discrepancies between their U.S. and European platforms. This allowed them to issue unintended refunds, causing significant financial losses. Sophisticated Tactics: The hackers demonstrated expertise and cunning by leveraging a flaw in the system, enticing users to make purchases knowing they would be rejected. This enabled swift cash withdrawals from ATMs, inflicting substantial harm on Revolut. Technical Details Concealed: While investigations continue, the specific technical details of the vulnerability remain undisclosed. It is crucial for Revolut and the industry to enhance their defenses against sophisticated cyber threats by embracing robust cybersecurity measures. Financial Fallout and Recovery Efforts: The cyberattack led to a total loss of approximately $20 million, with some funds successfully recovered. However, Revolut incurred a significant net loss, impacting their neobanking and fintech operations. Recent Arrests Shed Light: Coinciding with the breach disclosure, the arrest of a suspected senior member of the hacking group OPERA1ER highlights the interconnected nature of cybercriminal activities targeting financial institutions and mobile banking services. Effective Cybersecurity Practices:
Conclusion: The Revolut breach underscores the importance of fortifying defenses against evolving cyber threats. By adopting effective cybersecurity practices and leveraging specialized solutions, organizations can strengthen their security posture, mitigate risks, and protect valuable data. Armoryze stands ready to support organizations in their journey towards comprehensive cybersecurity. Contact us to learn more about our tailored services and solutions.
0 Comments
Progress Software has uncovered another critical SQL injection vulnerability in the MOVEit Transfer application, marking the third such vulnerability since the initial discovery. This blog highlights the details of the latest vulnerability, its similarities to previous flaws exploited by the Clop ransomware group, and the steps taken by Progress Software to address the issues.
Conclusion: While Progress Software has provided patch updates to mitigate the risks posed by these vulnerabilities, relying solely on patches may not offer comprehensive protection. Armoryze, a specialized cybersecurity company, offers risk-based vulnerability services to enhance your organization's security posture. Schedule a FREE consultation to strengthen your cyber defenses and safeguard critical assets. Armoryze specializes in risk-based vulnerability services that go beyond traditional patching. Assess your organization's security posture, identify vulnerabilities, and receive tailored recommendations to mitigate risks effectively. Schedule a FREE consultation today to strengthen your cyber defenses and protect critical assets. Protecting Photovoltaic Monitoring Systems from Cyber Attacks: Best Practices and Security Measures6/7/2023 Photovoltaic (PV) monitoring and diagnostic systems play a crucial role in the management of renewable energy production units. However, security researchers are sounding the alarm that tens of thousands of these systems are vulnerable to cyber attacks due to their exposure on the public web. In this blog post, we will explore the risks associated with these exposed systems and provide recommendations to enhance their security and protect against potential hackers.
Conclusion: The exposure of tens of thousands of PV monitoring systems on the public web poses a significant risk to the renewable energy sector. Security measures such as strong credentials, multi-factor authentication, regular updates, and network segregation can significantly enhance the protection of these systems against potential cyber attacks. By implementing these best practices, PV system administrators can safeguard their infrastructure, mitigate the risks, and contribute to the overall security of the renewable energy industry. At Armoryze, we understand the critical importance of securing your infrastructure against cyber threats. Our risk-based vulnerability management service provides comprehensive solutions to identify, prioritize, and remediate vulnerabilities in your systems. With our expertise and cutting-edge technology, we help organizations proactively manage their security posture and stay ahead of potential risks. Don't leave your PV monitoring systems vulnerable to attacks. Contact Armoryze today to learn more about how our services can help protect your infrastructure and ensure the uninterrupted operation of your renewable energy production units. In a relentless wave of cyber threats sweeping across Europe, Chinese hackers have launched a highly sophisticated and alarming phishing campaign known as SmugX, relentlessly targeting European government entities. This blog article exposes the insidious tactics employed by the campaign, sheds light on the threat actor behind it, and underscores the urgent need for robust cybersecurity measures.
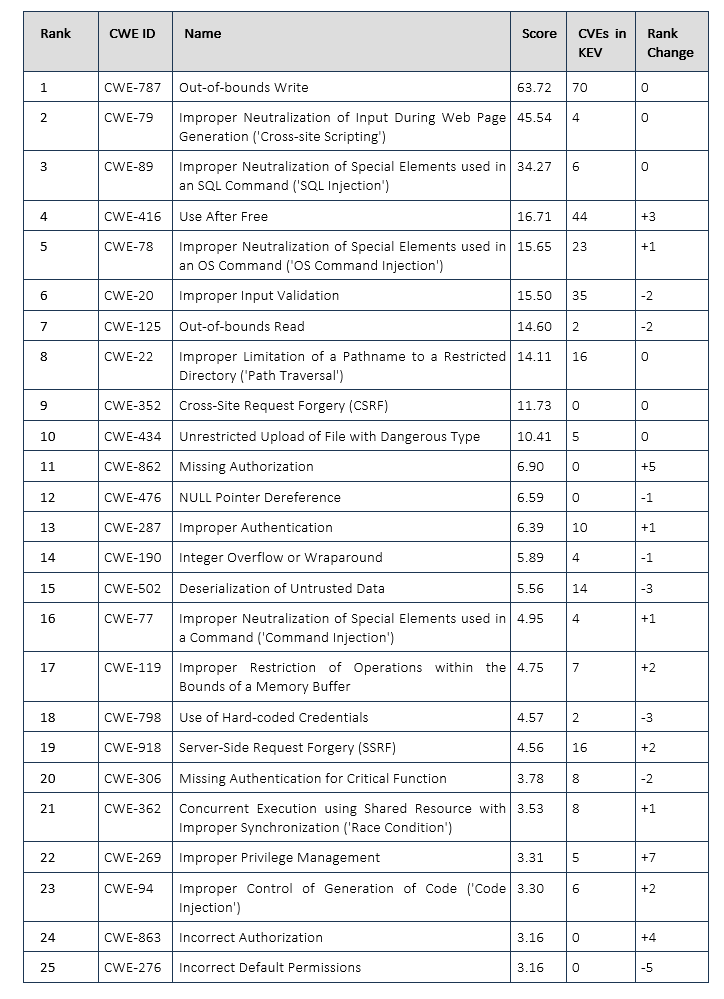
The Targeted Entities: Since December 2022, SmugX has specifically set its sights on embassies and foreign affairs ministries across Europe, including the United Kingdom, France, Sweden, Ukraine, Czech Republic, Hungary, and Slovakia. These calculated assaults on European institutions demand immediate attention and proactive defense. Decoding the SmugX Attack Chains: Security researchers have meticulously analyzed the SmugX attacks, uncovering two primary infection chains utilized by the campaign. Understanding the intricacies of these attack chains is crucial in comprehending the gravity of the threat they pose to organizations. SMUGX Variant 1- ZIP Archive and DLL Sideloading: SmugX leverages a devious approach involving a ZIP archive to deploy its malicious payload. This attack begins when unsuspecting victims open a ZIP file, triggering the execution of PowerShell. As a result, the contents of the archive are extracted and stored in a temporary folder on the Windows operating system. The archive contains three files, including a seemingly legitimate program known as either "robotaskbaricon.exe" or "passwordgenerator.exe." However, these innocent-looking files conceal a malicious DLL named "Roboform.dll." Loaded by the legitimate program through DLL sideloading, the Roboform.dll file unleashes a dangerous remote access trojan (RAT) called PlugX. Once executed, this RAT provides attackers with remote control over the victim's compromised system, enabling unauthorized access and potential data theft. SMUGX Variant 2- HTML Smuggling and MSI Download: In another variant of the SmugX attack, the threat actors employ HTML smuggling to stealthily download a JavaScript file from their server. This JavaScript file, upon execution, triggers the download of an MSI file, establishing a new folder in a specific location on the victim's computer. Within this folder, the attackers place three files: a modified legitimate program, a loader DLL, and an encrypted malicious payload called 'data.dat.' To avoid detection, the attackers utilize DLL sideloading to load the malicious payload into the computer's memory. By creating a hidden directory to store the legitimate program and malicious DLL files, the attackers further conceal their activities. Additionally, they add the program to the 'Run' registry key, ensuring its automatic execution upon system boot. As an added layer of deception, the PlugX malware may display a misleading PDF file to divert suspicion and reduce the chances of detection. The Notorious PlugX Remote Access Trojan (RAT): At the heart of the SmugX campaign lies the infamous PlugX RAT, a modular remote access trojan associated with Chinese advanced persistent threat (APT) groups since 2008. This highly adaptable malware empowers threat actors with capabilities like file exfiltration, screenshot capture, keylogging, and remote command execution. Although PlugX has been utilized by cybercriminal actors, the version employed in the SmugX campaign exhibits remarkable similarities to recent Chinese adversary attacks. The use of the RC4 cipher instead of XOR indicates a growing interest among Chinese threat groups in European targets, pointing towards espionage as the likely motive. Conclusion: The SmugX campaign poses a grave threat to European government entities, underscoring the pressing need to bolster cybersecurity measures. As a leading cybersecurity company committed to safeguarding our clients and mitigating risks, Armoryze stands ready to track and analyze emerging threats. At Armoryze, we offer cutting-edge SIEM logging and monitoring services that proactively detect and respond to potential security breaches. Our team of cybersecurity specialists is dedicated to assessing your organization's security posture and developing tailored security solutions aligned with your specific needs and requirements. Safeguard your critical assets and protect your reputation by partnering with Armoryze. Schedule a FREE consultation with our cybersecurity specialists today to fortify your defenses against sophisticated cyber threats. Don't wait until it's too late. Contact us now to take the first step towards a more secure future. Stay vigilant, keep your systems updated, and together let's protect your organization from the evolving cyber threat landscape. MITRE has recently unveiled its highly anticipated list of the top 25 most perilous software bugs. These vulnerabilities have plagued software systems over the past two years, posing severe threats to the security and stability of affected devices. In this article, we will explore the critical weaknesses highlighted by MITRE and shed light on their potential impact. By understanding these risks, we can take proactive measures to safeguard our systems from malicious actors and their harmful exploits. Software weaknesses encompass various flaws, bugs, vulnerabilities, and errors that can compromise the integrity and security of the systems they reside in. These weaknesses provide malicious actors with potential entry points to gain control over affected devices, extract sensitive data, or cause denial-of-service states. To raise awareness about these critical issues, MITRE has evaluated 43,996 CVE entries from the National Vulnerability Database (NVD) and CISA's Known Exploited Vulnerabilities (KEV) catalog, focusing on vulnerabilities discovered and reported between 2021 and 2022. After meticulous analysis, MITRE has assigned scores to each weakness based on their severity and prevalence. By normalizing the frequency and severity values relative to the dataset, MITRE has developed a ranking formula to determine the top 25 most dangerous software bugs. The severity is measured using the Common Vulnerability Scoring System (CVSS) score, ensuring a comprehensive evaluation of each vulnerability's impact. The Top 25 Dangerous Bugs: These vulnerabilities have been identified as the most dangerous due to their significant impact and widespread occurrence in software released over the past two years. Successful exploitation of these weaknesses can grant attackers complete control over targeted systems, enable them to exfiltrate sensitive data, or trigger debilitating denial-of-service (DoS) attacks. By sharing this list, MITRE aims to provide crucial information to the wider community, urging immediate attention to these critical software security weaknesses.
Conclusion: MITRE's recent unveiling of the top 25 most dangerous software bugs offers invaluable insights into the vulnerabilities that threaten our systems. It is essential for individuals, organizations, and developers to prioritize addressing these weaknesses promptly. By staying vigilant and implementing robust security measures, we can fortify our software systems against potential breaches, protect sensitive data, and maintain the integrity of our digital environments. Armoryze, a trusted leader in cybersecurity, understands the critical importance of safeguarding your systems against these dangerous software bugs. With our comprehensive Managed Security Services, we offer tailored solutions to proactively identify, mitigate, and protect against vulnerabilities and potential cyber threats. Our team of experienced professionals will work closely with you to develop a robust security strategy, implement proactive monitoring, and ensure the ongoing protection of your valuable assets. Don't leave your systems vulnerable to malicious attacks. Take action today and leverage the expertise of Armoryze Managed Security Services to fortify your defenses against the top software vulnerabilities highlighted by MITRE. Contact us now to schedule a consultation and secure your digital infrastructure. Remember, the battle against cyber threats requires constant vigilance. Stay informed, stay protected, and stay one step ahead with Armoryze security services. BlackCat Ransomware Exploits WinSCP Search Ads to Distribute Cobalt Strike: A Comprehensive Analysis4/7/2023 In a recent alarming development, the BlackCat ransomware group, also known as ALPHV, has taken advantage of malvertizing campaigns to deceive unsuspecting users. By utilizing search ads, they entice individuals into visiting counterfeit pages that closely mimic the official website of WinSCP, a widely-used file-transfer application for Windows. However, instead of providing legitimate installers, these fraudulent pages distribute files infected with malware. This article delves into the tactics employed by the BlackCat ransomware group, sheds light on the potential risks faced by system administrators and IT professionals, and reveals the subsequent stages of the attack.
1. Exploiting the Popularity of WinSCP: WinSCP (Windows Secure Copy) is a highly regarded, free, and open-source file-transfer application for Windows. It offers secure file transfer functionality using various protocols such as SFTP (SSH File Transfer Protocol), FTP (File Transfer Protocol), SCP (Secure Copy Protocol), and Amazon S3. Apart from its file transfer capabilities, WinSCP functions as a file manager, allowing users to navigate and manage files on remote servers or cloud storage. Renowned for its user-friendly interface, encryption capabilities, and support for automation and scripting, WinSCP has gained immense popularity among system administrators, web admins, and IT professionals. Recognizing this, the BlackCat ransomware group has exploited the application's reputation to gain initial access to valuable corporate networks. 2. The Deceptive Strategy: To carry out their nefarious activities, BlackCat ransomware operators have initiated ad campaigns on major search engines, including Google and Bing. When users search for "WinSCP Download," the manipulated search results display malicious links that are given priority over the legitimate WinSCP download sites. Unsuspecting victims, oblivious to the risks involved, click on these ads and are directed to websites posing as tutorials on automated file transfers using WinSCP. These deceptive sites have been meticulously designed to evade detection by Google's anti-abuse crawlers. 3. Cloned Websites and Malware Distribution: Upon reaching the counterfeit tutorial sites, victims come across clone websites that closely mimic the official WinSCP website. These clones employ domain names that bear a striking resemblance to the legitimate winscp.net domain, such as winsccp[.]com. In order to deceive users into downloading malware, the clone websites present a download button. Upon clicking the button, an ISO file containing "setup.exe" and "msi.dll" is downloaded. While "setup.exe" serves as a decoy to entice users, "msi.dll" acts as the malware dropper, triggered by the executable. 4. Execution and Malicious Payload: Once the victim executes "setup.exe," it invokes "msi.dll" to extract a Python folder from the DLL RCDATA section. This folder masquerades as a genuine WinSCP installer and is intended to be installed on the victim's machine. Furthermore, the installation process includes a trojanized python310.dll file and establishes a persistence mechanism by creating a run key named "Python" with the value "C:\Users\Public\Music\python\pythonw.exe." The executable pythonw.exe loads an obfuscated and modified python310.dll, which contains a Cobalt Strike beacon that establishes a connection with a command-and-control server. 5. Advanced Tools and Lateral Movement: Having gained a foothold through the Cobalt Strike beacon, the BlackCat ransomware group proceeds with their malicious activities. Trend Micro's analysts have identified the usage of various tools and techniques during the subsequent attack phases:
These advanced tools and techniques allow the BlackCat ransomware group to perform lateral movement within the compromised network, gather sensitive information, escalate privileges, and maintain persistence, thereby enabling them to carry out their malicious objectives effectively. It is crucial for system administrators, IT professionals, and users to remain vigilant and take proactive measures to protect their systems from such attacks. Implementing robust security measures, keeping software and applications up to date with the latest patches, and regularly educating users about potential risks and safe browsing practices are essential steps in mitigating the threat posed by the BlackCat ransomware group and similar malicious actors. In conclusion, the BlackCat ransomware group's exploitation of search ads to distribute Cobalt Strike via counterfeit WinSCP websites highlights the evolving tactics employed by cybercriminals. By capitalizing on the popularity of trusted applications and leveraging advanced tools, these threat actors can infiltrate corporate networks and cause significant harm. Staying informed, implementing effective security measures, and promoting a culture of cybersecurity awareness are crucial in safeguarding against such attacks. In the face of evolving cyber threats like the BlackCat ransomware group, it's vital to ensure the security of your systems. Armoryze offers a comprehensive Managed Detection and Ransomware Service that can help safeguard your organization against such attacks. Our expert team employs advanced threat intelligence, proactive monitoring, and rapid incident response to detect and mitigate ransomware threats. With Armoryze, you can have peace of mind knowing that your systems are protected by cutting-edge technology and experienced professionals. Don't wait until it's too late. Take action today and fortify your defenses against ransomware attacks. Contact us to learn more about our Managed Detection and Ransomware Service and to schedule a FREE consultation. Together, we can ensure the security and resilience of your organization's digital infrastructure. A critical security flaw, known as CVE-2023-3460, has been recently discovered in the widely used ‘Ultimate Member’ plugin, posing a serious concern for website owners. This vulnerability allows attackers to add unauthorized user accounts to the administrators group, granting them elevated privileges. Since June, this bug has been actively exploited, resulting in the creation of suspicious and unauthorized accounts. As a result, more than 200,000 WordPress websites are currently at risk due to this critical security vulnerability. The flaw exposes websites to ongoing attacks and poses a significant threat to site owners.
Understanding the ‘Ultimate Member' Plugin: The 'Ultimate Member' plugin is designed to streamline the registration and login processes on WordPress sites. It enhances the user experience by offering features such as user profile creation, role definition, custom form fields, and member directories. Exploiting the Vulnerability: The 'Ultimate Member' plugin contains a critical security flaw, tracked as CVE-2023-3460. This flaw allows attackers to create unauthorized user accounts with administrator-level privileges. Users of the plugin have reported the creation of suspicious accounts since June, indicating active exploitation of this vulnerability. Description: Ultimate Member <= 2.6.6 – Privilege Escalation via Arbitrary User Meta Updates Affected Plugin: Ultimate Member – User Profile, Registration, Login, Member Directory, Content Restriction & Membership Plugin Plugin Slug: ultimate-member Affected Versions: <= 2.6.6 CVE ID: CVE-2023-3460 CVSS Score: 9.8 (Critical) In simpler terms, the vulnerability in the 'Ultimate Member' plugin enables hackers to gain unauthorized access and control over websites by creating accounts with administrator-level privileges. Website owners must promptly address this issue to protect their websites and prevent further unauthorized access. Root Cause of the Issue: The vulnerability in the 'Ultimate Member' plugin can be attributed to a conflict between the plugin's blocklist logic and how WordPress handles metadata keys. WordPress is a popular content management system (CMS) used for creating and managing websites. Metadata keys are information tags attached to data that provide additional context and description. The plugin utilizes blocklists to store metadata keys that should not be altered to maintain data integrity. During account creation, the plugin cross-checks specific keys against these blocklists. However, attackers have exploited the discrepancy between the plugin and WordPress. By manipulating metadata keys, including the one responsible for storing user role and capabilities, they gain unauthorized access and manipulate the system. This operational disparity has allowed them to bypass the plugin's security measures and carry out malicious activities. Patching Efforts and Acknowledgment: The maintainers of the 'Ultimate Member' plugin have attempted to address the vulnerability in the last two plugin versions. However, these attempts have not fully patched the flaw. Nonetheless, the plugin maintainers have acknowledged the ongoing exploitation of the vulnerability in real-world scenarios. Mitigation Measures for Site Owners: To protect their websites from potential exploitation, site owners are strongly advised to disable the 'Ultimate Member' plugin. This step will help prevent further compromise resulting from the vulnerability. Additionally, site owners should conduct a thorough audit of administrator roles to identify any rogue accounts that might have been created. Conclusion: The discovery of a critical security vulnerability CVE-2023-3460 in the 'Ultimate Member' plugin puts more than 200,000 WordPress websites at risk. Site owners need to understand the seriousness of the issue, including its root cause and the ongoing exploitation by attackers. By promptly disabling the vulnerable plugin and conducting thorough website audits, site owners can mitigate the potential impact of these security risks. Protecting WordPress websites from potential cyber attacks and safeguarding user data should be the top priority. To achieve this, site owners are encouraged to prioritize security measures and implement robust security solutions. Armoryze offers comprehensive web application and API protection services, as well as risk-based vulnerability management services. These services can fortify your website's defenses and proactively identify, detect and prevent vulnerability exploitation. Don't wait for an attack to happen. Schedule a FREE consultation with Armoryze today to discuss your specific security needs and develop a tailored strategy to protect your WordPress website. By partnering with us and taking proactive steps, you can ensure the safety and integrity of your website and the data it holds. In recent times, cybersecurity researchers have uncovered a new and sophisticated Android malware called Fluhorse. This malware stands out due to its innovative approach of embedding malicious components directly into Flutter-based code. Flutter, an open-source UI toolkit developed by Google, enables developers to create interactive and feature-rich mobile applications across various platforms using a single codebase.
The Unique Characteristics of Fluhorse: Fluhorse has gained attention for its ability to camouflage itself within legitimate-looking apps, making it challenging for users to detect its presence. Its primary objective is to pilfer sensitive information, including user credentials, credit card details, and two-factor authentication (2FA) codes received via SMS. Initially detected in early May 2023, Fluhorse primarily targets users in East Asia by masquerading as popular applications like ETC and VPBank Neo. By assuming the guise of trusted apps, Fluhorse maximizes its chances of infecting devices. The malware predominantly spreads through phishing attacks, underscoring the importance of user awareness and caution while interacting with online content. A Noteworthy Encryption Technique and Vulnerability: Fluhorse employs OpenSSL's EVP cryptographic API for encryption and decryption, making it resistant to reverse engineering attempts. The malware encrypts its payload using the AES-128-CBC encryption algorithm. However, its susceptibility to decryption lies in the utilization of a hard-coded string for the key and initialization vector (IV). Security researchers can potentially exploit this vulnerability to decrypt the payload. Unveiling the Payload and its Functionality: Once decrypted, the payload is revealed as a ZIP file containing a Dalvik executable (.dex) file. The Dalvik executable, commonly employed in Android applications, is installed on infected devices. In the case of Fluhorse, this executable listens to incoming SMS messages and forwards them to a remote server under the control of threat actors. The Implications and Future Concerns: The ability to reverse engineer Flutter applications marks a significant breakthrough for antivirus researchers. However, it also raises concerns regarding the potential rise of more malicious Flutter apps in the future. To counter threats like Fluhorse effectively, organizations should adopt proactive security measures. Proactive Security Measures:
In conclusion, Fluhorse represents a significant and evolving Android malware threat that exploits Flutter-based apps as a disguise. To safeguard your organization's sensitive data, it is crucial to adopt proactive security measures. Stay vigilant, educate your employees, fortify authentication mechanisms, and implement robust endpoint security solutions. Additionally, enhance your defense strategy by partnering with Armoryze and leveraging our Managed Detection and Response (MDR) service. Armoryze's MDR service goes beyond traditional security measures by providing continuous monitoring, threat detection, and rapid incident response. Our team of cybersecurity experts combines advanced technologies with human intelligence to identify and neutralize threats in real-time. By integrating Armoryze MDR into your security framework, you can enhance your organization's ability to detect and respond to sophisticated malware attacks like Fluhorse. In a recent announcement, Microsoft has revealed a concerning rise in credential-stealing attacks orchestrated by the Russian state-affiliated hacker group, Midnight Blizzard. These intrusions, targeting governments, IT service providers, NGOs, defense, and critical manufacturing sectors, utilize residential proxy services to conceal the origin of the attacks. Formerly known as Nobelium and tracked under various aliases like APT29, Cozy Bear, Iron Hemlock, and The Dukes, Midnight Blizzard gained global attention following the SolarWinds breach in 2020. Despite being exposed, they continue to employ unseen tactics, making them a formidable force in the realm of espionage.
Sophisticated Tactics: Microsoft, in a series of tweets, detailed the techniques employed by APT29, including password spray, brute-force, and token theft methods. Additionally, the group leverages session replay attacks to gain initial access to cloud resources, capitalizing on stolen sessions potentially acquired through illicit means. Furthermore, APT29 relies on residential proxy services to obfuscate connections, making scoping and remediation challenging for victims. Their ability to adapt and persist highlights their determination to operate undeterred. New Spear-Phishing Campaign: Recorded Future recently uncovered a spear-phishing campaign orchestrated by APT28, targeting government and military entities in Ukraine since November 2021. Exploiting vulnerabilities in the Roundcube webmail software, these attacks aimed to gather intelligence through reconnaissance. A successful breach enabled the deployment of rogue JavaScript malware, redirecting emails and stealing contact lists. The campaign exhibited high levels of preparedness, utilizing news-related lures to exploit recipients' trust. Continued Threats and Hybrid Conflict: The identified activities align with another wave of attacks utilizing a then-zero-day flaw in Microsoft Outlook (CVE-2023-23397). This vulnerability was addressed in March 2023, but it emphasizes the persistent efforts of Russia-based threat actors targeting European organizations. The findings underscore the ongoing quest for valuable intelligence on Ukrainian and European entities, especially following the country's invasion in 2022. Notably, these cyber warfare operations have witnessed the deployment of wiper malware, showcasing one of the earliest instances of large-scale hybrid conflict. Conclusion: The rise of sophisticated cyber threats orchestrated by Russian state-affiliated hacker groups such as Midnight Blizzard and APT29 highlights the urgent need for robust cybersecurity measures. Organizations across various sectors must fortify their defenses to protect sensitive data and mitigate potential risks. At Armoryze, we understand the evolving threat landscape and offer a comprehensive solution to safeguard your business. Our Managed Detection and Response (MDR) services go beyond traditional measures, providing continuous monitoring, real-time threat detection, and swift action to mitigate risks. By partnering with Armoryze, you gain peace of mind knowing that your systems are under constant surveillance, and any threats or breaches are promptly addressed. Our expert team leverages advanced technologies and industry-leading practices to proactively defend your organization against cybercriminals. Don't leave your business vulnerable to sophisticated attacks. Schedule a FREE consultation with Armoryze today and fortify your security defenses. Remember, staying one step ahead of cybercriminals is crucial in today's digital landscape. Contact Armoryze now and let us help you safeguard your valuable assets. Unveiling Mockingjay: Evading EDR Detection with a Sophisticated Process Injection Technique27/6/2023 In the rapidly evolving landscape of cybersecurity threats, a highly advanced process injection technique called "Mockingjay" has emerged, posing a significant challenge to conventional security measures like Endpoint Detection and Response (EDR). This blog aims to delve into the intricacies of Mockingjay, its capability to bypass EDR detection, and the implications it holds for organizations. By gaining a comprehensive understanding of this advanced technique, businesses can adopt a holistic security approach to effectively counter the evolving threat landscape. The Mockingjay Technique: Recently discovered by the cybersecurity firm Security Joes, the Mockingjay process injection technique leverages legitimate Dynamic Link Libraries (DLLs) with read, write, and execute (RWX) sections to silently inject malicious code into remote processes, thereby evading EDR hooks and other security products. DLLs are files that contain reusable code and data which multiple programs can simultaneously use. What sets Mockingjay apart from other approaches is its ingenious avoidance of commonly abused Windows API calls, special permissions, memory allocation, and thread initiation. By bypassing these typical detection opportunities, Mockingjay establishes a robust and reliable environment for executing its injection technique without detection. Development of Mockingjay: The dedicated researchers at Security Joes embarked on a mission to identify a vulnerable DLL with a default RWX section that could be modified to load malicious code without raising suspicion from security software. Their investigation led them to the DLL msys-2.0.dll within Visual Studio 2022 Community, which boasted a default RWX section of 16 KB. To implement the Mockingjay technique, the team developed two injection methods: self-injection and remote process injection. In the case of self-injection, a custom application called "nightmare.exe" loads the vulnerable DLL directly into its memory space, exploiting two Windows API calls ("NtAllocateVirtualMemory" and "NtWriteVirtualMemory") to gain access to the RWX section without the need for memory allocation or permission changes. This injection method bypasses EDR hooks using the "Hell's Gate EDR unhooking" technique, allowing the injected shellcode to execute without detection. The second method involves exploiting the RWX section of msys-2.0.dll to inject a payload into a remote process, specifically targeting the "ssh.exe" process. The custom application launches "ssh.exe" as a child process, establishes a handle to the target process, and injects the malicious code into the RWX memory space of the vulnerable DLL. The injected shellcode then loads the "MyLibrary.dll" DLL file, enabling the establishment of a reverse shell connection with the attacker's machine. Notably, this remote injection attack successfully evades EDR solutions without requiring new thread creation, memory allocation, or permission changes. Why Mockingjay Eludes Detection:
Mockingjay's effectiveness lies in its ability to operate covertly, evading traditional EDR solutions. While EDRs typically monitor Windows APIs such as 'WriteProcessMemory,' 'NtWriteVirtualMemory,' 'CreateRemoteThread,' or 'NtCreateThreadEx,' which are commonly invoked in traditional process injection attacks, Mockingjay avoids triggering these typical alarms. By sidestepping the usual detection mechanisms, Mockingjay significantly reduces the likelihood of raising suspicion. Examples of Process Injection Techniques: Process injection techniques include DLL injection, PE (portable executable) injection, reflective DLL injection, thread execution hijacking, process hollowing, mapping injection, APC (asynchronous procedure call) injection, and more. These techniques exploit vulnerabilities in the target process to inject malicious code and execute it within the context of a legitimate process, bypassing security measures. Conclusion: The emergence of Mockingjay as a highly sophisticated process injection technique underscores the urgent need for organizations to adopt a comprehensive security approach. Relying solely on traditional EDR solutions is no longer sufficient in the face of advanced threats like Mockingjay. At Armoryze, we recognize the evolving cybersecurity landscape and offer Managed Detection and Response (MDR) services that go beyond standard measures. Our team of experts is equipped to protect your organization from the ever-changing threat landscape. Don't leave your business vulnerable to sophisticated attacks. Schedule a FREE consultation with Armoryze today and take proactive steps to fortify your security defenses. With our advanced MDR services, you can gain peace of mind knowing that your systems are continuously monitored, threats are detected in real-time, and swift action is taken to mitigate risks. Stay one step ahead of cybercriminals--contact us now and secure the future of your organization. |
- Home
- Solutions
- Services
-
Company
- About Us
- Secure Your Future with Armoryze
- Customer Success Story
-
Free Resources
>
- Win With Armoryze
- Whitepaper - How To Prioritize Risk Across the Attack Surface
- The Ultimate Guide to Achieving Cyber Essentials Plus Certification
- ISO 27001 Implementation Checklist
- Whitepaper - What is Credential Stuffing? How To Prevent Credential Stuffing Attacks.
- eBook: Effective Security Strategies for Devops & Application Services
- eBook - How To Build A Next Generation SOC
- Free Cyber Security Assessment & Consultation
- Free Trial >
- Careers >
- Contact Us
- Blog
- Privacy-Policy
- SHOP