|
Introduction:
In the realm of modern computing, Unified Extensible Firmware Interface (UEFI) plays a pivotal role as a critical software standard. Despite its significance, UEFI often goes unnoticed by most users. Serving as a vital link between hardware and operating systems, UEFI replaces the traditional BIOS format and is essential to the functioning of most computers. However, cyber attackers have discovered and exploited flaws in UEFI implementations, granting them persistence in compromised systems even after defensive measures are taken. In response to recent incidents like the BlackLotus malware, Armoryze joins the Cybersecurity and Infrastructure Security Agency (CISA) in highlighting the importance of bolstering UEFI cybersecurity. This blog post will shed light on the significance of UEFI software, the challenges posed by UEFI attacks, and actionable steps to enhance UEFI security. UEFI: Powering Modern Computing: UEFI serves as the dominant firmware software standard, responsible for managing the physical computing machinery upon which all other components rely. It facilitates the seamless transition from powering on a device to booting the operating system, while also orchestrating the harmonious functioning of various hardware elements like processors, hard drives, graphics cards, USB ports, and Wi-Fi antennas. UEFI as a Vulnerable Attack Surface: The appeal of targeting UEFI software lies in the significant advantages it offers attackers. UEFI comprises various components, including security and platform initializers, drivers, bootloaders, and power management interfaces. Attackers can exploit vulnerabilities in these components to achieve persistence, allowing them to maintain control even after a system reboot or operating system reinstallation. Bolstering UEFI Security: To safeguard against UEFI attacks effectively, the UEFI community must prioritize secure by design practices and mature Product Security Incident Response Team (PSIRT) operations. Integrating PSIRTs with UEFI software development, quality assurance testing, and update distribution teams can significantly reduce the impact of threats like BlackLotus. Actionable Steps to Improve UEFI Cybersecurity: A comprehensive approach is necessary to strengthen UEFI cybersecurity and protect against evolving threats. Armoryze recommends the following steps to fortify UEFI security:
Conclusion: With adversaries becoming more adept at exploiting UEFI vulnerabilities, the urgency to enhance UEFI cybersecurity cannot be understated. By embracing secure by design practices and prioritizing PSIRT maturity, the UEFI community can reduce the impact of UEFI attacks and safeguard critical computing systems. Immediate action is crucial, and it starts with collaboration and implementation of the proposed solutions. Armoryze, alongside CISA, encourages the UEFI community to adopt these measures vigorously, beginning today. Together, we can create a safer computing environment and thwart cyber threats against UEFI software. Found this article interesting? Follow us on LinkedIn and Twitter to read more latest security updates and exclusive content we post.
0 Comments
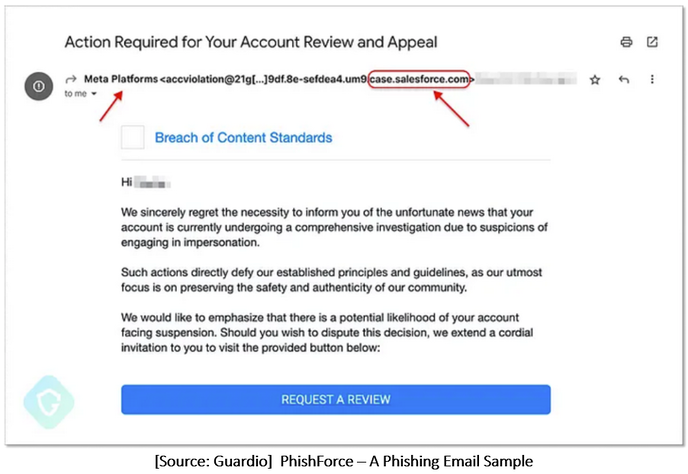
PhishForce Unleashed: How Salesforce Email Services Were Exploited to Phish Facebook Accounts4/8/2023 Introduction: In the realm of cybersecurity, a sophisticated phishing campaign known as 'PhishForce' has emerged, sparking concern among experts. Cybercriminals have found ingenious ways to dodge email filters and manipulate our trust in legitimate services, camouflaging malicious emails within trustworthy email gateway services. Little do we know that these very gateways can be misused by bad actors to wreak havoc. The Salesforce Phishing Email: A Masterpiece of Deception This phishing campaign raised eyebrows when highly convincing Facebook phishing emails surfaced, addressing recipients by their real names and posing as "Meta Platforms." Equipped with a seemingly innocent blue button, the emails led users to a phishing page designed to harvest Facebook account details. The Intricate Web of Exploitation:
To make matters worse, the attackers harnessed the power of Salesforce's Email-To-Case feature to gain control over legitimate @salesforce.com email addresses, making their phishing emails appear genuine and trustworthy. The Vulnerability Unraveled: The attackers manipulated the Salesforce email validation process to access emails sent to specific @salesforce.com addresses and obtain verification links for their malicious campaigns. Guardio's Responsible Disclosure and Swift Response: Upon discovering the severity of the vulnerability by Guardio, responsible disclosure was followed, and Salesforce acted promptly to address the issue. As of the 28th of July ’23, the vulnerability was resolved, and a comprehensive fix was deployed across all Salesforce services and instances. The Facebook Connection: The PhishForce campaign had yet another sinister aspect. The attackers exploited legacy web game canvases under Facebook's ecosystem to directly insert malicious content into the platform. Top Three Best Recommendations to Safeguard Against Salesforce Phishing Emails: 1. Employee Awareness and Training: Conduct regular security awareness training for all employees, educating them about the latest phishing tactics, including the PhishForce campaign. Teach them to be cautious when clicking on links or downloading attachments from unknown sources. Training should also cover how to identify phishing indicators and report suspicious emails. 2. Email Security Solutions: Implement advanced email security solutions that utilize machine learning algorithms and artificial intelligence to identify and block phishing emails. These solutions can help detect and quarantine suspicious emails before they reach employees' inboxes, providing an essential layer of defense against PhishForce and other phishing attempts. 3. Multi-Factor Authentication (MFA): Enforce multi-factor authentication for accessing sensitive systems and applications, including Salesforce. MFA adds an extra layer of security by requiring users to provide additional authentication factors beyond passwords, making it harder for attackers to gain unauthorized access even if credentials are compromised. By focusing on these top three recommendations, organizations can significantly enhance their cybersecurity posture and protect against PhishForce and similar phishing campaigns. Employee education, robust email security, and multi-factor authentication are essential components of a strong defense against evolving cyber threats. Real-World Impact and Armoryze's Solution: Phishing attacks continue to evolve, exploiting seemingly legitimate services like CRMs and cloud-based platforms for malicious purposes. Vigilance and proactive measures from organizations like Armoryze help mitigate the impact of such campaigns. At Armoryze, we are committed to fortifying your digital assets against evolving threats. Our email security and managed security services offer real-time threat detection, vulnerability management, security incident response, managed endpoint protection, threat hunting, compliance and regulatory support, security awareness training, security strategy, and consulting to ensure your organization's cybersecurity. Conclusion: The "PhishForce" campaign showcased the intricate techniques employed by threat actors to exploit trusted services like Salesforce for nefarious purposes. Responsible disclosure and swift action by industry players proved crucial in mitigating the impact of this campaign. At Armoryze, we are committed to empowering your organization with cutting-edge protection against cyber threats. Schedule a FREE consultation today to discover how our tailored Managed Security Services can secure your digital future and keep your web assets safe from evolving threats. Together, we will ensure your organization remains ahead in the battle against sophisticated cyber-attacks. Introduction:
In an era where digital transformation is driving businesses to adopt cloud technologies, the security of cloud environments has become a paramount concern. Cyber security researchers at Mitiga have uncovered a disruptive new threat landscape, shaking the foundation of Amazon Web Services (AWS). In a startling revelation, they have exposed how malicious actors can exploit the AWS Systems Manager Agent (SSM Agent) as a Remote Access Trojan (RAT) on both Linux and Windows environments. This ingenious technique enables attackers to gain covert control over endpoints, evading traditional security measures and laying the groundwork for a range of malicious activities. The Cloud: A New Frontier for Threat Actors: As organizations migrate their critical workloads to cloud infrastructures like AWS, threat actors have swiftly adapted to exploit this expanding attack surface. The AWS Systems Manager Agent (SSM Agent), designed as a legitimate tool for admins to manage their instances, has now become the weapon of choice for malevolent actors seeking to operate under the radar. A Stealthy Threat Unveiled: The AWS SSM Agent as a RAT: Our ground breaking research highlights how a threat actor with elevated privilege access on a compromised endpoint can subvert the SSM Agent's original purpose, transforming it into a silent Remote Access Trojan (RAT). This insidious transformation allows attackers to maintain persistent access, undetected, and perform a myriad of malicious activities on the compromised system. The Advantages for Attackers: 1. Camouflaged as Legitimate Software: The SSM Agent binary is signed by Amazon, making it appear as approved software to Antivirus (AV) and Endpoint Detection & Response (EDR) solutions, thus evading immediate detection. 2. No Additional Malware Deployment: Attackers can utilize the existing SSM Agent on the target system, eliminating the need to upload and execute new RAT binaries that may trigger security alarms. 3. Command and Control Flexibility: Adversaries can use their malicious AWS account as a Command and Control (C&C) server, making their communication look genuine and harder to trace. 4. Minimal Infrastructure Requirements: Attackers solely rely on the SSM service and agent, reducing the need for elaborate attack infrastructure. 5. Broad Control over Endpoints: Features like "RunCommand" and "StartSession" in the SSM Agent provide attackers with effortless control over compromised endpoints, granting them extensive operational authority. Attacker Techniques: 1. Scenario 1 - Hijacking the SSM Agent: In this scenario, the attacker registers the SSM Agent to run in "hybrid" mode with a different AWS account, enabling it to communicate with the attacker's account and execute commands. This method ensures that the SSM Agent appears to run as a legitimate process, making it challenging for traditional security solutions to detect any anomalous behavior. 2. Scenario 2 - Running Another SSM Agent Process: In this approach, the threat actor launches a second SSM Agent process, separate from the original one, to communicate with their AWS account while the legitimate agent continues to work with the original AWS account. By cleverly using Linux namespaces or running the agent in "container" mode on Linux and setting environment variables on Windows, the attacker maintains control over the compromised endpoint without impacting the original agent's operation. 3. Abusing the SSM Proxy Feature: Threat actors can route SSM traffic to an attacker-controlled server without relying on AWS infrastructure by manipulating environment variables like "http_proxy" and "https_proxy." This sneaky tactic allows them to leverage the SSM Agent while avoiding detection by AWS services. Detection and Recommendations: 1. AV and EDR Solutions: Remove SSM Agent binaries from the allow list to improve detection capabilities and analyze potential malicious activities. 2. Implement Detection Techniques: Monitor instance data changes, track multiple agent processes, and review CloudTrail logs to detect suspicious actions. 3. Restrict Command Receipt: Use the VPC endpoint for Systems Manager to ensure EC2 instances only respond to commands from the original AWS account or organization. 4. SIEM and SOAR Integration: Integrate detection techniques into Security Information and Event Management (SIEM) and Security Orchestration, Automation, and Response (SOAR) platforms to proactively hunt for threats. 5. Stay Informed: Keep abreast of emerging threat landscapes and consult with cybersecurity experts to fortify your organization's security posture. Conclusion: The potential misuse of AWS SSM Agent as a Remote Access Trojan poses a significant threat to endpoint security in the cloud era. By understanding the tactics employed by threat actors and embracing proactive cybersecurity strategies, organizations can safeguard their AWS environments effectively. At Armoryze, we are dedicated to empowering businesses with cutting-edge security solutions and expertise to stay ahead of the evolving threat landscape. Take Action with Managed Detection & Response (MDR) Service: To ensure your organization's resilience against emerging threats, we offer our state-of-the-art Managed Detection & Response (MDR) service. Our expert security analysts work tirelessly to detect, respond, and neutralize threats in real-time. With our MDR service, you gain 24/7 monitoring, threat hunting, and incident response, allowing you to focus on your core business operations while we fortify your cybersecurity defenses. Empower Growth with Armoryze: In today's digital landscape, security is not just a necessity; it's a strategic advantage. Armoryze empowers businesses to thrive securely, protecting their digital assets and customer trust. Don't wait for the threat to strike; take proactive measures with Armoryze's MDR service and embrace security to enable growth and innovation. Together, we can build an impenetrable defense against the rising tide of cyber threats. Embrace security, empower growth with Armoryze. Contact us today to secure your cloud environment and safeguard your organization from the ever-evolving cyber threats. References: https://www.mitiga.io/blog/mitiga-security-advisory-abusing-the-ssm-agent-as-a-remote-access-trojan In today's rapidly evolving digital landscape, cybersecurity remains a paramount concern for organizations worldwide. In response to recent events, Ivanti, a leading IT software company, has acted swiftly by issuing an urgent warning to its customers regarding a second zero-day vulnerability discovered in its widely-used product, Endpoint Manager Mobile (EPMM). This critical flaw, already exploited in targeted attacks, has sent shockwaves through the cybersecurity community, emphasizing the significance of being vigilant and proactive in defending against potential threats. Safeguarding digital assets and protecting sensitive information are now critical imperatives for businesses.
A New Zero-Day Threat: A zero-day vulnerability is a security flaw that is unknown to the software vendor, leaving no time for them to develop a patch before it gets exploited. On July 24, 2023, Norwegian authorities disclosed that numerous government ministries fell victim to a cyberattack involving the exploitation of the following vulnerabilities in Ivanti's EPMM:
The Dangers of Remote File Write Vulnerabilities: Remote File Write (RFW) vulnerabilities pose grave risks to system security. Attackers can exploit these loopholes to create, modify, or delete files on a victim's system from a remote location, potentially leading to data breaches and complete system takeovers. The Combined Exploitation: To exacerbate the situation, threat actors have been observed leveraging the CVE-2023-35081 vulnerability in combination with CVE-2023-35078 to bypass admin authentication and access control list (ACL) restrictions. This technique enables them to execute malicious OS commands on the appliance as the tomcat user. The sophisticated nature of these attacks suggests a possible state-sponsored threat actor, although the exact identity of the attackers remains uncertain. Taking Prompt Action with Armoryze: Protecting your systems is of utmost importance. Armoryze offers a FREE consultation for our Risk-based Vulnerability Management Service, designed to help your organization fortify its cyber defenses. Don't wait until it's too late; schedule your consultation now, and our experts will assist you in safeguarding your digital assets. The Urgent Need for Action: If you are an Ivanti Endpoint Manager Mobile (EPMM) user, regardless of the version, you are at risk. The impacted versions include 11.4 releases 11.10, 11.9, and 11.8, as well as older releases. The severity of these vulnerabilities has led Ivanti and CISA to issue alerts, urgently advising organizations to apply patches immediately. To safeguard your systems against the latest zero-day exploits, follow these steps:
As of now, the attackers behind these exploits remain unidentified, but the evidence suggests they may be state-sponsored threat actors. Given the large number of potentially vulnerable internet-exposed systems and the availability of proof-of-concept (PoC) code for CVE-2023-35078, the risk of further exploitation is significant. Take the First Step Towards Security: As a leading cybersecurity company, Armoryze is dedicated to safeguarding businesses from such threats. We understand the importance of risk-based vulnerability management and offer a comprehensive service tailored to your organization's needs. By scheduling a FREE consultation with our experts, you can take the first step towards securing your systems against the latest zero-day exploits. Conclusion: The discovery of the second zero-day vulnerability in Ivanti EPMM highlights the ever-evolving landscape of cybersecurity threats. Remaining vigilant and adopting proactive security measures is paramount for organizations. Armoryze is ready to assist you in protecting your digital assets. Don't wait for an attack to happen—act now and schedule a FREE consultation to strengthen your defenses against potential cyber threats. In today's ever-changing cybersecurity landscape, the activities of one nation-state actor have garnered significant attention from the cybersecurity community. APT31, also known as Bronze Vinewood, Judgement Panda, and Violet Typhoon, is suspected to have ties to China and has orchestrated a series of sophisticated attacks on industrial organizations in Eastern Europe. Their primary objective: extracting valuable data from air-gapped systems. In this article, we will delve into the tactics employed by APT31, explore their diverse range of implants, and provide valuable insights on how Armoryze MDR can effectively safeguard your organization against these advanced threats.
APT31's Intrusions: A Closer Look APT31 has demonstrated remarkable versatility, employing a variety of tools categorized into three distinct stages:
Kaspersky's team has uncovered over 15 distinct implants and their variants utilized by APT31. These implants can be broadly categorized into three groups: those that establish remote access, collect sensitive data, and transmit the pilfered information to infrastructure controlled by the threat actors. Of particular concern is a sophisticated modular malware capable of profiling removable drives and contaminating them with a worm, facilitating data exfiltration from isolated air-gapped networks of industrial organizations in Eastern Europe. Unveiling the APT31 Backdoors: 1. Meatball Backdoor: Among the newly discovered backdoors, Meatball stands out with its extensive remote access capabilities, tailored for both x86 and x64 systems. This versatile backdoor executes a plethora of tasks, including listing processes, devices, and disks, performing file operations, capturing screenshots, utilizing remote shells, and even self-updating. To further its control, Meatball creates a service named "esetcss" or adds itself to the registry key "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\esetcss," ensuring automatic execution during OS startup. 2. FourteenHi Backdoor: A formidable malware family identified during the ExCone campaign, FourteenHi targets government entities and industrial organizations alike. Its sophisticated features encompass file manipulation, command execution, reverse shells, and self-erasure, making it a potent weapon in the hands of APT31. Expanding Horizons: Linux Infiltration While APT31 has predominantly focused on Windows environments, recent evidence suggests a growing interest in Linux systems. Notably, South Korean companies experienced attacks employing the Rekoobe backdoor, evading detection through encryption and enabling malicious file downloads and internal data theft. Defense Against APT31 with Armoryze MDR: As the looming threat of APT31 continues to evolve, safeguarding your organization necessitates a comprehensive and proactive approach. Armoryze MDR stands ready to fortify your cybersecurity defenses with our cutting-edge security solutions, including:
Conclusion: As the elusive APT31 poses multifaceted intrusions on air-gapped systems in Eastern Europe, the need for vigilant cybersecurity measures becomes paramount. Armoryze MDR stands steadfast in its commitment to protect your organization from APT31 and other advanced adversaries. With our proactive and robust security solutions, you can safeguard your critical assets, maintain business continuity, and fortify your reputation. Contact Armoryze MDR today, and together, we will build a secure and resilient future for your organization in the face of ever-evolving cyber threats. In a recent alert by the Cybersecurity and Infrastructure Security Agency (CISA), a new and dangerous malware called "Submarine" has come to light. This malware was specifically designed to infiltrate Barracuda ESG (Email Security Gateway) appliances, posing a significant threat to federal agencies' networks. The attackers responsible for this breach took advantage of a previously unknown vulnerability known as CVE-2023-2868, enabling them to conduct data-theft attacks without detection.
At Armoryze, we take cybersecurity seriously, and incidents like this highlight the importance of staying proactive in safeguarding your organization against such threats. Our Risk-Based Vulnerability Management Service is designed to delve deep into the insights of vulnerabilities like CVE-2023-2868 and provide you with comprehensive protection against potential exploits. By partnering with us, you can fortify your defenses and prevent malicious actors from gaining unauthorized access to your systems. Protect your business with Armoryze and stay ahead of cyber threats. The Attack Timeline: The attacks were detected in May, but it appears they have been active since at least October 2022. The attackers targeted the Barracuda ESG appliances by exploiting the CVE-2023-2868 remote command injection zero-day vulnerability. They used this opportunity to deploy various malware components, including Submarine, Saltwater, SeaSpy, and SeaSide, to establish reverse shells for easy remote access. Key Findings:
Response from Barracuda: After the attacks were identified, Barracuda took proactive measures to mitigate the impact on its customers. They issued a warning and provided replacement devices at no charge to affected customers instead of merely re-imaging them with new firmware. However, the attackers responded with another malware strain, Submarine, to maintain persistent access on customer ESG appliances. Details about Submarine Malware: Submarine is a type of backdoor that has different parts and works within a database called Structured Query Language (SQL) on the ESG appliance. This backdoor can do several things like carrying out commands with high-level access, staying hidden for a long time, managing commands, and cleaning up its traces. CISA also found some related files attached to emails using Multipurpose Internet Mail Extensions (MIME). These files contained sensitive information taken from the compromised SQL database. Details of malware components:
Advice for Affected Customers: If you suspect your Barracuda ESG appliance has been compromised, it's essential to discontinue its use and seek assistance from Barracuda support. They recommend obtaining a new ESG virtual or hardware appliance to replace the compromised one. Security Recommendations: In light of this incident, it's crucial for users and administrators to consider using the following best practices to strengthen the security posture of their organization's systems. Any configuration changes should be reviewed by system owners and administrators prior to implementation to avoid unwanted impacts.
Conclusion: The emergence of Submarine malware and its successful exploitation of the CVE-2023-2868 vulnerability highlights the importance of proactive cybersecurity measures. Protecting your organization against such threats requires vigilant monitoring, timely patching, and a strong security strategy. At Armoryze, we understand the criticality of cybersecurity and offer Managed Security services to help safeguard your business from cyber threats. Schedule a FREE consultation with our expert team today to fortify your cybersecurity defenses. Schedule Your FREE Consultation Today! Don't let cyber threats compromise your business. Take action now and schedule a FREE consultation with our Cybersecurity experts. Let us assess your organization's security posture and recommend tailored Managed Security services to mitigate risks effectively. Empower your business with the best defense against cyberattacks. Contact us and stay one step ahead of potential threats with Armoryze. Your cybersecurity is our priority! In today's fast-changing digital world, cybersecurity is crucial to keep our virtual assets safe from lurking threats. Today, we'll explore Ubuntu Linux and a serious security concern known as "GameOver(lay)". It involves two vulnerabilities, CVE-2023-2640 and CVE-2023-32629, discovered by Wiz security team. The two vulnerabilities are found in the widely-used OverlayFS module, a popular part of Linux used in containers, which are like virtual boxes for apps. In this context, having a reliable risk-based vulnerability management service, like the one offered by Armoryze, can play a significant role in enhancing security measures. Such services help organizations identify and prioritize potential vulnerabilities, making it easier to protect critical systems from potential exploits like "GameOver(lay)." By understanding the vulnerability risks and addressing them proactively, businesses can bolster their cybersecurity defenses and ensure a safer digital environment for their valuable assets. Understanding the GameOver(lay) CVEs: CVE-2023-2640: On Ubuntu kernels carrying both c914c0e27eb0 and "UBUNTU: SAUCE: overlayfs: Skip permission checking for trusted.overlayfs.* xattrs", an unprivileged user may set privileged extended attributes on the mounted files, leading them to be set on the upper files without the appropriate security checks. CVE-2023-32629: Local privilege escalation vulnerability in Ubuntu Kernels overlayfs ovl_copy_up_meta_inode_data skip permission checks when calling ovl_do_setxattr on Ubuntu kernels A Closer Look at OverlayFS: OverlayFS is a special type of filesystem that allows one filesystem to be placed on top of another without changing the original. This is particularly useful in container setups, where it keeps the base image intact while allowing for changes to be made easily. However, this flexibility also makes OverlayFS attractive to hackers as it creates a potential entry point for attacks. GameOver(lay) takes advantage of vulnerabilities that have existed in OverlayFS for some time. This means the same tricks used in past attacks can be used again without any changes. This makes the current vulnerabilities even more dangerous because attackers can easily use old methods that are well-known and readily available. The journey into GameOver(lay) vulnerabilities started with changes made to the OverlayFS module in Ubuntu back in 2018. Initially, these modifications seemed harmless and didn't raise any concerns. However, as the Linux project made further changes, unforeseen consequences began to unravel, leading to the discovery of vulnerabilities that demand our attention. Important Dates in the Vulnerability Chain: 1. January 29, 2018: Ubuntu made a decision to use an internal implementation (__vfs_setxattr_noperm) for setting extended attributes, without realizing the implications it would have for future events. 2. December 14, 2020: Linux discovered and addressed a new vulnerability in OverlayFS, adding stronger protections to the vfs_setxattr function. However, Ubuntu's continued reliance on __vfs_setxattr_noperm left a vulnerable flow unresolved. 3. April 28, 2022: Linux introduced further modifications to OverlayFS, resulting in a second vulnerable flow that shared the same root cause. These dates mark crucial milestones in the vulnerability chain, highlighting the sequence of events that ultimately led to the discovery of the vulnerabilities we are currently addressing. Who is vulnerable? Identifying the vulnerable parties can be challenging due to the numerous releases available for Ubuntu. However, our research team has successfully pinpointed the impacted versions, which are as follows: Vulnerability Detection & Mitigation Strategies:
Protecting against these vulnerabilities requires two key steps: establishing a user namespace and an OverlayFS mount. This means attackers would need to execute code on the targeted system, making remote attacks unlikely. To stay safe, Ubuntu users should upgrade to the fixed versions of the impacted kernels (see the list above) as soon as possible. If upgrading is not immediately possible, an alternative solution is to limit the user namespace usage to users with restricted privileges to prevent potential exploitation. To apply this restriction, use the command: sudo sysctl -w kernel.unprivileged_userns_clone=0 For those who want the protection to persist after restarting the system, run this command: echo kernel.unprivileged_userns_clone=0 | \ sudo tee /etc/sysctl.d/99-disable-unpriv-userns.conf Additionally, organizations can take advantage of advanced Armoryze risk-based vulnerability management service to gain valuable insights into potential risks and vulnerabilities. By leveraging such proactive measures, businesses can enhance their cybersecurity defenses, ensuring a secure digital environment without compromising on performance or efficiency. Conclusion: In the face of ever-evolving cybersecurity threats, it is imperative to remain vigilant and proactive in safeguarding our digital assets. The vulnerabilities uncovered in Ubuntu Linux's OverlayFS module, known as GameOver(lay), underscore the importance of risk-based vulnerability management services, like the one offered by Armoryze. By understanding the intricacies of kernel interactions and the implications of open-source project modifications, we can empower our defenders with the knowledge they need to protect against potential adversaries. GameOver(lay) reminds us that even the most trusted and widely-used software can be vulnerable, emphasizing the need for continuous monitoring and proactive measures. Upgrading to fixed versions, implementing user namespace restrictions, and leveraging advanced vulnerability management services are essential steps in mitigating risks effectively. At Armoryze, we are committed to helping businesses strengthen their cybersecurity defenses through our risk-based vulnerability management service. By scheduling a FREE consultation with our team, you can gain valuable insights into your organization's potential vulnerabilities and take action to address them proactively. Let us work together to fortify our defenses and create a safer digital environment for all. With Armoryze at your side, you can confidently face future challenges and stay ahead of emerging threats. Protecting your valuable assets is not just a responsibility; it's a necessity in today's fast-changing digital world. Take the first step towards a more secure future by scheduling your FREE consultation with Armoryze today. Together, we can ensure a resilient and secure cyber landscape for your organization and beyond. References: https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2023-32629 https://lists.ubuntu.com/archives/kernel-team/2023-July/140920.html https://wiz.io/blog/ubuntu-overlayfs-vulnerability https://ubuntu.com/security/notices/USN-6250-1 Introduction:
In the ever-evolving landscape of cybersecurity threats, a recent discovery has sent shockwaves through the industry. Meet "Decoy Dog," a formidable malware that has taken the foundation of the Pupy RAT, an open-source remote access trojan, and transformed it into a sophisticated and highly potent threat. Today, we delve into the depths of this malicious entity, revealing it’s never-before-seen capabilities that have left experts astonished. The origins of Decoy Dog remain unclear as yet, but it's suspected to be operated by a handful of nation-state hackers, who employ distinct tactics but respond to inbound requests that match the structure of client communication. Decoy Dog makes use of the domain name system (DNS) to perform command-and-control (C2). An endpoint that's compromised by the malware communicates with, and receives instructions from, a controller (i.e., a server) via DNS queries and IP address responses. Java Code Execution and Sophisticated Communication: The malware has the ability to execute arbitrary Java code on client systems, adding an extra layer of complexity to its attacks. Furthermore, the malware employs a mechanism akin to a traditional DNS domain generation algorithm (DGA) to connect with emergency controllers. This innovative communication technique involves Decoy Dog domains designed to respond to replayed DNS queries from compromised clients, making it even more challenging to detect and combat. According to Dr. Burton, head of threat intelligence at Infoblox, Decoy Dog outperforms its predecessor Pupy, with a command to redirect communication from the current controller to an alternative one, detected through statistical analysis of DNS queries. Understanding the DGA, DNS Server, and Pupy:
Decoy Dog Threat Actors' Swift Adjustments and Ongoing Threat: The threat actors behind the operation are said to have made swift adjustments to their attack infrastructure in response to the earlier disclosures, taking down some of the DNS nameservers as well as registering new replacement domains to establish remote persistence. The first known deployment of Decoy Dog dates back to late-March or early-April 2022, following which three other clusters were detected as under the control of different controllers. Below web domains have been associated with Decoy Dog malware: cbox4.ignorelist.com rcmsf100.net nsdps.cc maxpatrol.net j2update.cc hsdps.cc claudfront.net atlas-upd.com allowlisted.net Conclusion: The rise of Decoy Dog malware has exposed the constantly evolving and sophisticated nature of cyber threats directed at enterprise networks. Armoryze, a prominent cybersecurity company, is steadfast in its commitment to staying ahead of such dangers and protecting businesses from potential data breaches and disruptions. Through in-depth analysis of Decoy Dog and other emerging malware, Armoryze can deliver effective solutions to counter these threats and ensure the safety of businesses. As the threat landscape continues to evolve, Armoryze remains dedicated to providing cutting-edge cybersecurity measures that safeguard their clients' valuable assets and operations. Armoryze: Your Shield Against Decoy Dog Malware As a pioneering MDR service provider, Armoryze stands ready to defend your business against the menacing Decoy Dog malware. Our proactive approach combines cutting-edge technology, threat intelligence, and expert analysis to identify and neutralize threats before they inflict damage. To protect your organization from the growing menace of advanced malware like Decoy Dog, take proactive steps by partnering with Armoryze for our Managed Detection and Response (MDR) service. Our MDR service combines cutting-edge technology, experienced professionals, and real-time monitoring to identify and neutralize threats before they cause harm. Don't wait until it's too late. Schedule a FREE consultation with our team of cybersecurity experts today. Together, we can fortify your network defenses and ensure your business remains resilient in the face of evolving cyber threats. Safeguard your assets, reputation, and customer trust with Armoryze's MDR service. Reach out to us now and stay one step ahead in the cybersecurity battleground. Introduction:
In the fast-paced digital world, where software development and project management thrive, Atlassian, an Australian software company serving software developers, project managers, and development teams, has taken swift action to address two critical remote code execution (RCE) vulnerabilities in Confluence Data Center and Server. Additionally, they have also mitigated another RCE vulnerability found in Bamboo Data Center. In this article, we will delve into the intricate details of these vulnerabilities, exploring the proactive measures that Atlassian has implemented to protect its users and the broader digital community. Armoryze: Empowering Your Cybersecurity Defense Armoryze, a leading expert in cybersecurity solutions, is dedicated to providing comprehensive protection and peace of mind to its extensive user base. Discover how Armoryze's commitment to vulnerability management empowers businesses to stay one step ahead of potential security risks, effectively safeguarding them from the potentially devastating consequences of cyberattacks. Critical Vulnerabilities in Confluence: Immediate Action Required Confluence, a widely-used collaboration software, is currently facing critical security vulnerabilities that require immediate attention. These vulnerabilities, classified as Remote Code Execution (RCE) and Injection flaws, pose severe risks to the confidentiality, integrity, and availability of the affected systems. Here's an overview of the identified vulnerabilities: CVE-2023-22505: Severity: High Affected Versions: Confluence Data Center & Server version 8.0.0 CVSS Score: 8 (Extremely dangerous) Description: This RCE vulnerability allows an authenticated attacker to execute arbitrary code without any user interaction, leading to potentially devastating consequences. CVE-2023-22508: Severity: High Affected Versions: Confluence Data Center & Server version 7.4.0 CVSS Score: 8.5 Description: This critical RCE vulnerability enables authenticated attackers to execute arbitrary code, posing severe consequences for confidentiality, integrity, and availability. Notably, it requires no user interaction, making it highly exploitable. Affecting Bamboo Data Center: In addition to the Confluence vulnerabilities, a related critical security flaw affects Bamboo Data Center version 8.0.0: CVE-2023-22506: Severity: High Affected Versions: Bamboo Data Center version 8.0.0 CVSS Score: 7.5 Description: This flaw combines Injection and RCE vulnerabilities, empowering authenticated attackers to modify system call actions and execute arbitrary code, posing severe risks to confidentiality, integrity, and availability. Urgent Patches Released: Protect Your Systems Now The developers responded promptly and released crucial updates for Confluence versions 8.3.2 and 8.4.0, effectively resolving both critical vulnerabilities. For organizations unable to upgrade immediately, it is highly recommended to update to at least version 8.2.0, as it contains the necessary patch for CVE-2023-22508. Taking these urgent actions will help safeguard the system and protect against potential security breaches. Discovery and Bug Bounty Program: Collaborative Cybersecurity Efforts Atlassian acknowledges the invaluable contributions of private users who discovered these vulnerabilities and reported them through the bug bounty program. This underscores the significance of collaborative efforts in enhancing cybersecurity and promoting responsible disclosure. Proactive Vulnerability Transparency: Atlassian's advisory emphasizes that the newly discovered vulnerabilities are the outcome of an extended scope in its vulnerability disclosure policies, which were previously focused primarily on first-party, critical-severity bugs. The proactive approach to vulnerability transparency ensures customers have the information they need to make informed decisions about updating products. Conclusion: Atlassian's rapid response and dedication to security highlight the critical role of proactive vulnerability management in today's digital landscape. As cyber threats continue to evolve, organizations must prioritize cybersecurity measures to protect their data, systems, and reputation. Consult Armoryze's Cybersecurity Specialists Preventing vulnerabilities requires a multifaceted approach. Regular software updates, robust access controls, security audits, employee training, and third-party risk assessments are essential elements of a comprehensive security strategy. Armoryze stands ready to be your trusted cybersecurity partner. Our risk-based vulnerability management services are tailored to suit your organization's specific needs, offering cutting-edge solutions to detect and mitigate potential risks effectively. Schedule a FREE consultation with our digital security specialists at Armoryze today and discover how our expertise can fortify your defenses against potential risks. Together, we can ensure a safer digital future for your organization. Stay protected, stay secure, and take the first step towards a robust cybersecurity posture by scheduling your FREE consultation with Armoryze. Protect what matters most - your business. Introduction:
In today's rapidly changing digital landscape, the security of your Linux systems is of utmost importance. The Qualys Threat Research Unit (TRU) has recently uncovered a critical remote code execution vulnerability in OpenSSH's forwarded ssh-agent, bringing this issue to the forefront. To protect your business from potential cyber threats, staying informed about the latest security concerns and implementing robust measures is essential. CVE-2023-38408: Unveiling the Critical Flaw: A significant security concern has been identified for OpenSSH users with CVE-2023-38408 (CVSS score: N/A). This vulnerability allows remote attackers to execute arbitrary commands on vulnerable hosts, necessitating immediate action to prevent exploitation. Understanding the Exploitation: SSH Agent and Libraries: A critical vulnerability has been discovered in SSH-agent's source code, enabling remote attackers with access to a user's forwarded ssh-agent on a remote server to load and unload shared libraries in /usr/lib* on the user's workstation. This vulnerability arises when SSH-agent is compiled with ENABLE_PKCS11, the default configuration. Exploiting four common side effects of shared libraries, attackers can achieve reliable, one-shot remote code execution in SSH-agent, posing a significant risk to its security, requiring immediate attention and patching. Urgent Updates for Ubuntu Desktop Users: Proof-of-concept testing revealed vulnerabilities in default installations of Ubuntu Desktop 22.04 and 21.10, but all OpenSSH users must update promptly to mitigate potential risks effectively, regardless of the Linux distribution. Fortify Your Systems Now: At Armoryze, safeguarding our clients' businesses is our top priority. We strongly urge all OpenSSH users to take immediate action and update their systems, thereby fortifying their defenses against potential cyber threats. Effective Measures to Address CVE-2023-38408: To protect against the vulnerability, follow these comprehensive steps:
Strengthen Your Defenses with Risk-Based Vulnerability Management: In today's evolving cyber landscape, comprehensive cybersecurity measures are crucial. Armoryze offers a cutting-edge Risk-Based Vulnerability Management service tailored to your specific needs, providing maximum protection against emerging threats. Take proactive steps to secure your business today! Conclusion: Safeguarding your Linux systems from potential vulnerabilities requires continuous effort. By promptly updating OpenSSH and engaging Armoryze's Risk-Based Vulnerability Management service, you can fortify your cybersecurity defenses and protect your digital assets. Partner with us to build a resilient defense against modern-day cyber threats. Schedule a FREE consultation with our experts and take the first step towards a secure future. |
- Home
- Solutions
- Services
-
Company
- About Us
- Secure Your Future with Armoryze
- Customer Success Story
-
Free Resources
>
- Win With Armoryze
- Whitepaper - How To Prioritize Risk Across the Attack Surface
- The Ultimate Guide to Achieving Cyber Essentials Plus Certification
- ISO 27001 Implementation Checklist
- Whitepaper - What is Credential Stuffing? How To Prevent Credential Stuffing Attacks.
- eBook: Effective Security Strategies for Devops & Application Services
- eBook - How To Build A Next Generation SOC
- Free Cyber Security Assessment & Consultation
- Free Trial >
- Careers >
- Contact Us
- Blog
- Privacy-Policy
- SHOP